Disabling VoIP Inspection
Description
This article is, about turning off SIP inspection on a FortiGate. It also talks about what happens when you do that.Disabling the VoIP inspection may influence the production systems. Re-enabling SIP-ALG will require a restart.
Disabling SIP-ALG is not the first Troubleshooting action to take. Do not perform this action unless proper troubleshooting is done first.
Fortinet says we should use SIP/SCCP proxy/ALG, which people call SIP-ALG in cases.This is what Fortinet recommends.The other option in FortiGate is SIP-helper.SIP-helper is a solution that just does a very basic job of opening up a pinhole.In some situations other companies say we should turn off the SIP inspection on the FortiGate.We need to be careful and check the date and the FortiGate model when we read these articles about FortiGate because they might be old.These articles, about FortiGate might be outdated.
Scope
Any supported version of FortiGate.
Solution
The use of an Application Layer Gateway (ALG) allows for:
1.Modification of IP addresses in the application payload when NAT is used.
2.Dynamic opening of data ports ('pinholes') as required to allow the audio traffic.
Otherwise, SIP-helper can open these ports with very basic Layer4 logic. Otherwise, firewall policies must be used to statically open a wide range of ports for RTP/audio (through a VIP).
3.Inspection and logging of VoIP traffic.For information on how SIP ALG works in FortiOS and how to fix SIP problems check out the other articles at the end of this article.You should only disable SIP ALG when you are trying to figure out a problem. This helps you isolate the issue.SIP ALG has settings that can help you fix problems with FortiGate or handle unusual SIP situations, in your VoIP setup. Look at these options before you disable SIP ALG.In FortiOS version 5.2 and later the FortiOS proxy handles all SIP traffic by default.In FortiOS version 5.0 if you do not apply a VoIP profile the SIP session helper will be used instead.The following diagram shows a general SIP call flow over FortiGate:
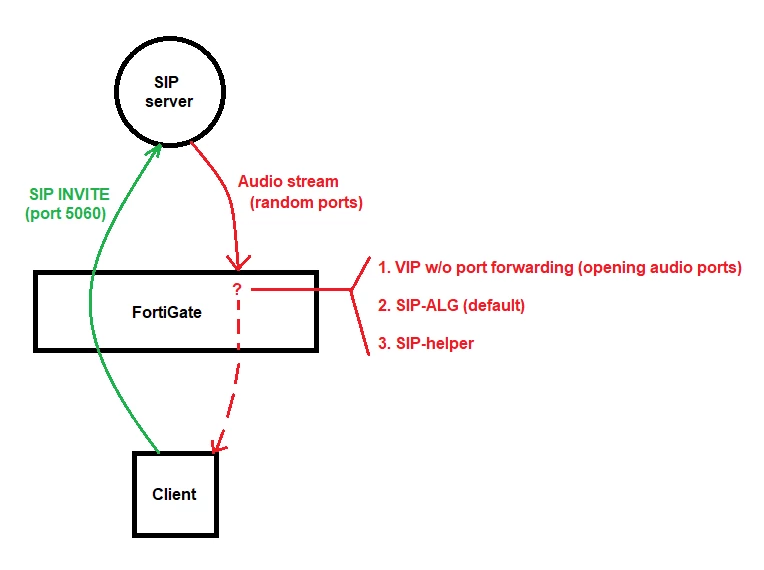
Disabling all VOIP inspection on the FortiGate prevents it from opening the RTP session and therefore, has no audio. When NAT is involved, FortiGate must use one of the three options above.
Preparation:
Before you turn off SIP ALG and SIP session helper you need to do these two things:
1.Modify the local SIP server configuration (if NAT is used).If the SIP traffic is NAT'd when passing through the FortiGate, the SIP server must be configured to use its public IP address in the application header. All other VoIP equipment must also refer to the SIP server by its public IP.
2.Open up corresponding audio ports (range) through VIP on the FortiGate.Firewall policies must now explicitly allow all UDP ports to be open for the audio traffic (and not only the SIP 5060 or SCCP 2000 control ports).
Note :
When a firewall policy has a voip-profile applied, SIP-ALG is used over the SIP session-helper, even if disabled. However, if the SIP config under the VOIP profile is set to disable, then in such a case, session helper will be used irrespective of ALG config.Disabling the SIP session-helper is only necessary if ALL the SIP inspection must be removed.The commands associated with the SIP-helper will not be relevant if the FortiGate is using SIP-ALG. Fine-tuning SIP-ALG is done through the VoIP profile.Multi-VDOM considerations: sip-helper is a global setting. Deleting sip-helper from a global context will make it inaccessible for all VDOMs. SIP-ALG is enabled (by default) and can be disabled per VDOM. VoIP profiles are not available when a FortiGate VDOM is configured in NGFW policy-based mode, and therefore cannot be used.
Step 1:
Follow the steps below to disable the SIP session-helper.Remove the corresponding session helper for SIP. Check the ID of the SIP session helper:config system session-helpershow
A similar setting to the following will appear among the displayed settings:
edit 13
set name sip
set protocol 17
set port 5060
next
end
Here, entry 13 points to SIP traffic, which uses UDP port 5060 for signaling.In this example, run the following commands to remove the corresponding entry:delete 13endNote that the SIP entry does not need to be 13. Cross-verify which entry has the SIP helper settings.
Step 2:
To make a change you need to disable the default voip alg mode.The voip alg mode is set to enable SIP-ALG by default.You can check this by using the show command to see the current settings, for the voip alg mode and SIP-ALG.So you have to change the default voip alg mode to disable SIP-ALG.config system settings
set default-voip-alg-mode proxy-based <-- Default value.
end
Run the following command to instruct the FortiGate to disable SIP-ALG (proxy-based)
and use SIP-helper (kernel-helper-based):config system settings
set default-voip-alg-mode kernel-helper-based
end
Note 1:
The command to set sip expectation to enable or disable is not meant to enable or disable the sip helper. It is actually used to control whether a pinhole is created or not as explained in the command help.The command help says that this command is used to enable or disable the helper that adds a dynamic SIP firewall allow rule. It also says that this command is used to enable or disable the SIP kernel session helper to create an expectation for port 5060 which's the port used by sip.So the command to set sip expectation to enable or disable is really about controlling the sip kernel session helper for sip. It is used to create an expectation, for port 5060 used by sip.
Note 2:
The command 'sip-nat-trace enable | disable' is not designed to enable | disable sip-helper. This command is in effect ONLY when SIP session-helper is used (ONLY when 'set default-voip-alg-mode kernel-helper-based' AND 'SIP session helper is present/not deleted'). As the command-help says: 'Enable/disable recording the original SIP source IP address when NAT is used'.
Note 3:
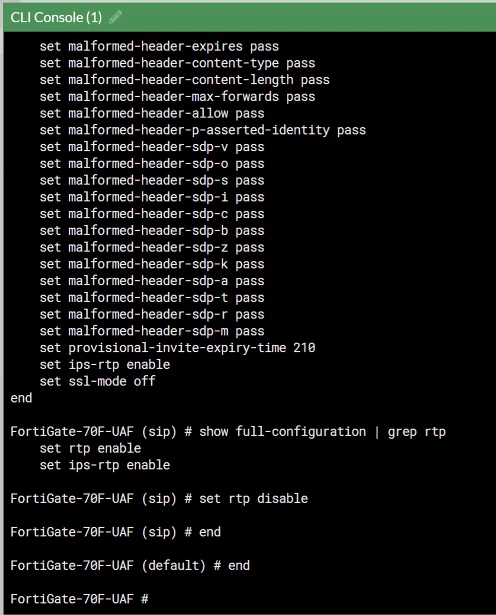
When the SIP ALG is turned on the FortiGate changes the address of the SIP signaling and the RTP media streams. It does this by making firewall rules.. Sometimes the SIP server already has a set of ports that it uses. If that is the case it can cause problems, like calls getting dropped. The media streams going to the wrong place. If you stop the FortiGate from handling the RTP it will only deal with the SIP signaling. This means the RTP media streams can go through without the FortiGate changing the ports of the RTP media streams. The FortiGate will focus on the SIP signaling sessions. Leave the RTP media streams alone.To configure RTP inspection bypass on a FortiGate, the following commands need to be executed:
config voip profile
edit default
config sip
set rtp disable
end
end
Step 3:
Either clear the sessions or reboot the FortiGate to ensure changes take effect.To clear the sessions, select the control session (port 5060) that will be cleared.Once the control session is ended, the RTP session is also ended.diagnose sys session filter dport 5060The command to clear the sessions applies to ALL sessions unless a filter (like above) is applied, and therefore will interrupt all traffic.diagnose sys session clearNote: Since this command could be very impactful, it is highly recommended to verify which sessions will be cleared.To do that, run the following command before the 'diagnose sys session clear': diagnose sys session filter diagnose sys session listAlternatively, reboot the FortiGate using either GUI or CLI. The CLI command is:execute rebootRebooting the FortiGate unit is often requested by TAC, as stale sessions may occasionally occur on the device.
Note:
It is also possible to disable SIP-ALG from the VoIP profile if needed (for example, when SCCP and SIP are both transiting the firewall and SCCP works ok).In this case, the SIP traffic will be handled by the SIP-helper even if the default-voip-alg-mode is set to proxy-based:
This allows SCCP to be handled by SIP-ALG and SIP by sip session-helper
config voip profile
edit default
config sip
set status disable
end
end
end
Disabling SIP session helper with VDOMs enabled.If VDOMs are enabled, disable the session helper from global as the session helper setting is a global parameter, and is not available under any particular VDOM. Since this is a global setting, removing or disabling the session-helper globally affects all the VDOMs.config global(global)# config system session-helperThere might be scenarios where a particular VDOM (VDOM-A, for example) has to use the session-helper settings for the SIP traffic processing, and VDOM-B needs to have the session-helper disabled so that SIP traffic passing through VDOM-B is not inspected by the SIP session-helper.In these or similar cases, use the following settings:
config firewall service custom
(custom) edit SIP-Helper-disable
(Helper-disable) set udp-portrange 5060(
Helper-disable) set helper disable
(Helper-disable) next
Once the above custom service with the helper set to disabled has been created, the same has to be called in the corresponding policy, which allows the SIP traffic.This will ensure that the firewall does not process the SIP traffic, provided the traffic hits the corresponding policy where the customer service named Helper-disable is applied.As proved by some isolated cases, this last method is not the best approach, as the sip-helper may be triggered by the traffic, even when the session-helper is disabled per service SIP-Helper-disable.
Note:
It is necessary to clear all of the sessions for port 5060 (clearing sessions using port 5060 will drop all of the active calls passing through FortiGate).
diagnose sys session filter clear
diagnose sys session filter dport 5060
diagnose sys session clear
diagnose sys session filter clear
diagnose sys session filter sport 5060
diagnose sys session clear
