Verifying FortiGuard Connectivity In FortiManager
Description
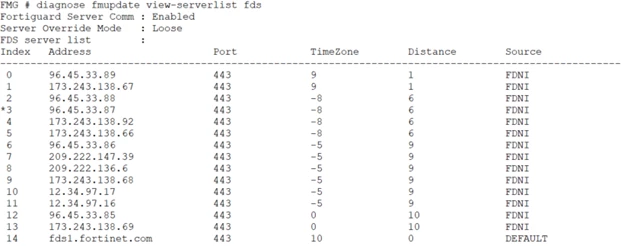
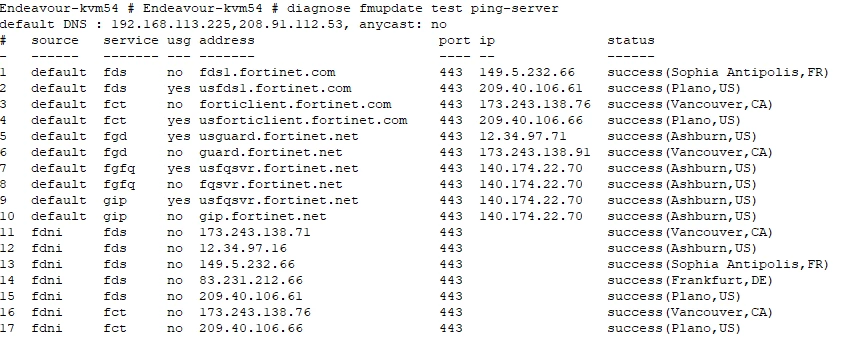
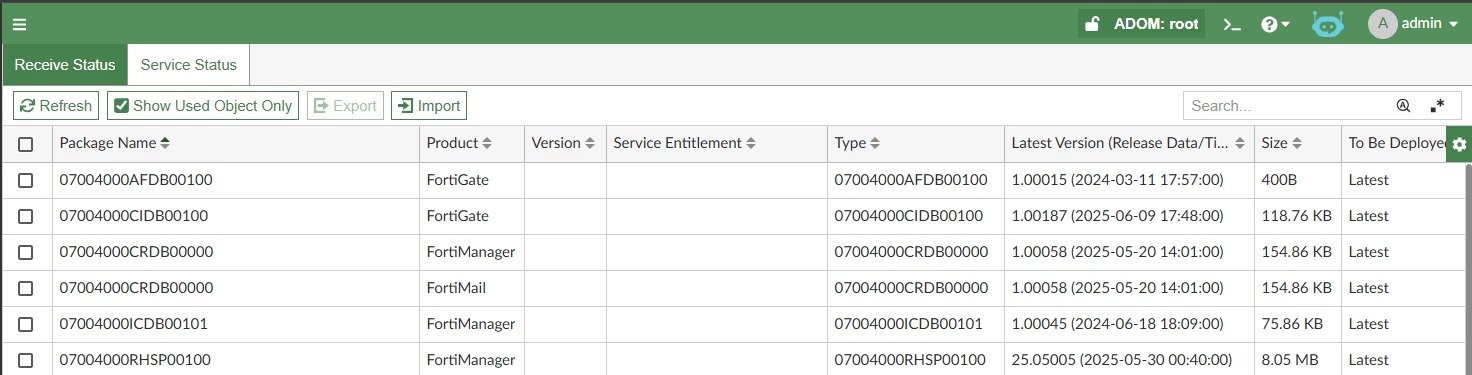
This article explains how to verify and troubleshoot FortiGuard connectivity in FortiManager, using anti-virus updates as an example.
Scope
FortiManager.
Solution